Schnorr Proof of Knowledge (PoK) for Discrete Logarithm. More...
#include "secp256k1_mpt.h"#include <string.h>#include <openssl/sha.h>#include <openssl/rand.h>#include <stdlib.h>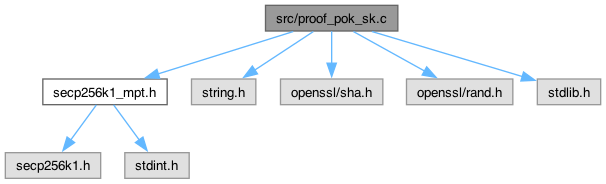
Go to the source code of this file.
Functions | |
| static int | pubkey_equal (const secp256k1_context *ctx, const secp256k1_pubkey *pk1, const secp256k1_pubkey *pk2) |
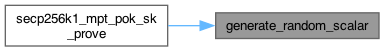
| static int | generate_random_scalar (const secp256k1_context *ctx, unsigned char *scalar) |
| static void | build_pok_challenge (const secp256k1_context *ctx, unsigned char *e_out, const secp256k1_pubkey *pk, const secp256k1_pubkey *T, const unsigned char *context_id) |
| int | secp256k1_mpt_pok_sk_prove (const secp256k1_context *ctx, unsigned char *proof_out, const secp256k1_pubkey *pk, const unsigned char *sk, const unsigned char *context_id) |
| int | secp256k1_mpt_pok_sk_verify (const secp256k1_context *ctx, const unsigned char *proof, const secp256k1_pubkey *pk, const unsigned char *context_id) |
Detailed Description
Schnorr Proof of Knowledge (PoK) for Discrete Logarithm.
This module implements a non-interactive zero-knowledge proof (NIZK) that allows a user to prove possession of the secret key sk corresponding to a public key pk, without revealing sk.
Protocol (Schnorr Identification Scheme):
Given a public key \( P = sk \cdot G \), the protocol proves knowledge of \( sk \). It is made non-interactive using the Fiat-Shamir transform.
- Commitment: Prover samples random nonce \( k \leftarrow \mathbb{Z}_q \) and computes:
\[ T = k \cdot G \]
- Challenge (Fiat-Shamir): The challenge \( e \) is derived deterministically:
\[ e = H(\text{"MPT_POK_SK_REGISTER"} \parallel P \parallel T \parallel \text{ContextID}) \]
- Response: Prover computes scalar:
\[ s = k + e \cdot sk \pmod{n} \]
- Verification: Verifier reconstructs \( e \) and checks:
\[ s \cdot G \stackrel{?}{=} T + e \cdot P \]
Security Context: This proof is used during account initialization/registration to prevent Rogue Key attacks (where an attacker registers a key constructed from another user's key to cancel it out) and to ensure the user actually controls the ElGamal key being registered.
- See also
- [Spec (ConfidentialMPT_20260201.pdf) Section 3.3.2] Proof of Knowledge of Secret Key
Definition in file proof_pok_sk.c.
Function Documentation
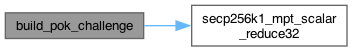
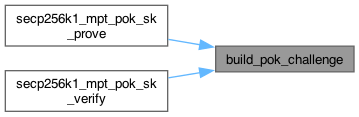
◆ build_pok_challenge()
|
static |
Definition at line 58 of file proof_pok_sk.c.
◆ generate_random_scalar()
|
static |
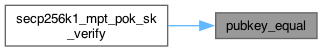
◆ pubkey_equal()
|
static |
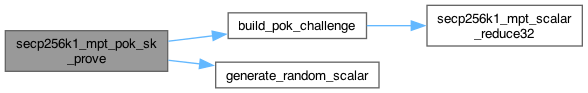
◆ secp256k1_mpt_pok_sk_prove()
| int secp256k1_mpt_pok_sk_prove | ( | const secp256k1_context * | ctx, |
| unsigned char * | proof, | ||
| const secp256k1_pubkey * | pk, | ||
| const unsigned char * | sk, | ||
| const unsigned char * | context_id ) |
Proof of Knowledge of Secret Key for Registration
Definition at line 92 of file proof_pok_sk.c.
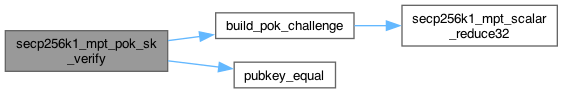
◆ secp256k1_mpt_pok_sk_verify()
| int secp256k1_mpt_pok_sk_verify | ( | const secp256k1_context * | ctx, |
| const unsigned char * | proof, | ||
| const secp256k1_pubkey * | pk, | ||
| const unsigned char * | context_id ) |