Zero-Knowledge Proof Linking ElGamal Ciphertexts and Pedersen Commitments. More...
#include "secp256k1_mpt.h"#include <openssl/sha.h>#include <openssl/rand.h>#include <string.h>#include <assert.h>#include <stdio.h>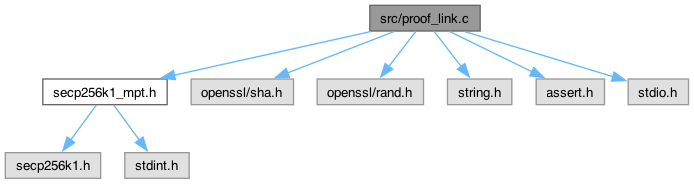
Go to the source code of this file.
Macros | |
| #define | SER_AND_HASH(pk_ptr) |
Functions | |
| static int | pubkey_equal (const secp256k1_context *ctx, const secp256k1_pubkey *pk1, const secp256k1_pubkey *pk2) |
| static int | generate_random_scalar (const secp256k1_context *ctx, unsigned char *scalar_bytes) |
| static void | build_link_challenge_hash (const secp256k1_context *ctx, unsigned char *e_out, const secp256k1_pubkey *c1, const secp256k1_pubkey *c2, const secp256k1_pubkey *pk, const secp256k1_pubkey *pcm, const secp256k1_pubkey *T1, const secp256k1_pubkey *T2, const secp256k1_pubkey *T3, const unsigned char *context_id) |
| int | secp256k1_elgamal_pedersen_link_prove (const secp256k1_context *ctx, unsigned char *proof, const secp256k1_pubkey *c1, const secp256k1_pubkey *c2, const secp256k1_pubkey *pk, const secp256k1_pubkey *pcm, uint64_t amount, const unsigned char *r, const unsigned char *rho, const unsigned char *context_id) |
| Proves the link between an ElGamal ciphertext and a Pedersen commitment. | |
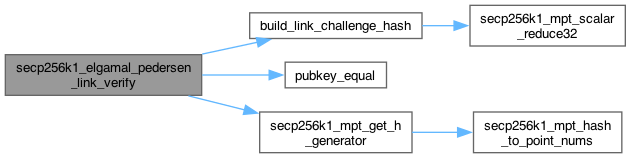
| int | secp256k1_elgamal_pedersen_link_verify (const secp256k1_context *ctx, const unsigned char *proof, const secp256k1_pubkey *c1, const secp256k1_pubkey *c2, const secp256k1_pubkey *pk, const secp256k1_pubkey *pcm, const unsigned char *context_id) |
| Verifies the link proof between ElGamal and Pedersen commitments. | |
Detailed Description
Zero-Knowledge Proof Linking ElGamal Ciphertexts and Pedersen Commitments.
This module implements a Sigma protocol to prove that an ElGamal ciphertext and a Pedersen commitment encode the same underlying plaintext value \( m \), without revealing \( m \) or the blinding factors.
Statement: The prover demonstrates knowledge of scalars \( (m, r, \rho) \) such that:
- \( C_1 = r \cdot G \) (ElGamal Ephemeral Key)
- \( C_2 = m \cdot G + r \cdot P \) (ElGamal Masked Value)
- \( PC_m = m \cdot G + \rho \cdot H \) (Pedersen Commitment)
Protocol (Schnorr-style):
- Commitment: Prover samples nonces \( k_m, k_r, k_\rho \) and computes:
- \( T_1 = k_r \cdot G \)
- \( T_2 = k_m \cdot G + k_r \cdot P \)
- \( T_3 = k_m \cdot G + k_\rho \cdot H \)
- Challenge:
\[ e = H(\text{"MPT_ELGAMAL_PEDERSEN_LINK"} \parallel C_1 \parallel C_2 \parallel P \parallel PC_m \parallel T_1 \parallel T_2 \parallel T_3 \parallel \dots) \]
- Response:
- \( s_m = k_m + e \cdot m \)
- \( s_r = k_r + e \cdot r \)
- \( s_\rho = k_\rho + e \cdot \rho \)
- Verification: Verifier checks:
- \( s_r \cdot G \stackrel{?}{=} T_1 + e \cdot C_1 \)
- \( s_m \cdot G + s_r \cdot P \stackrel{?}{=} T_2 + e \cdot C_2 \)
- \( s_m \cdot G + s_\rho \cdot H \stackrel{?}{=} T_3 + e \cdot PC_m \)
**Security Context:**
This proof prevents "bait-and-switch" attacks where a user sends a valid range proof for a small amount (e.g., 10) but updates the ledger balance with a large or negative amount (e.g., 1,000,000 or -5). It binds the two representations together.
- See also
- [Spec (ConfidentialMPT_20260201.pdf) Section 3.3.5] Linking ElGamal Ciphertexts and Pedersen Commitments
Definition in file proof_link.c.
Macro Definition Documentation
◆ SER_AND_HASH
| #define SER_AND_HASH | ( | pk_ptr | ) |
Function Documentation
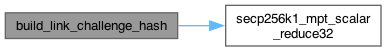
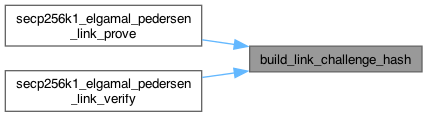
◆ build_link_challenge_hash()
|
static |
Definition at line 64 of file proof_link.c.
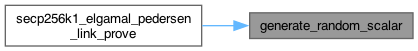
◆ generate_random_scalar()
|
static |
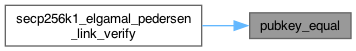
◆ pubkey_equal()
|
static |
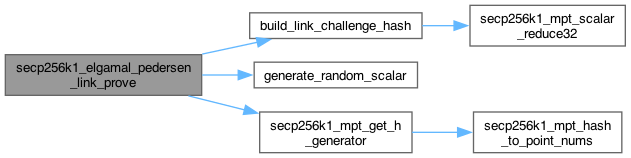
◆ secp256k1_elgamal_pedersen_link_prove()
| int secp256k1_elgamal_pedersen_link_prove | ( | const secp256k1_context * | ctx, |
| unsigned char * | proof, | ||
| const secp256k1_pubkey * | c1, | ||
| const secp256k1_pubkey * | c2, | ||
| const secp256k1_pubkey * | pk, | ||
| const secp256k1_pubkey * | pcm, | ||
| uint64_t | amount, | ||
| const unsigned char * | r, | ||
| const unsigned char * | rho, | ||
| const unsigned char * | context_id ) |
Proves the link between an ElGamal ciphertext and a Pedersen commitment.
- Formal Statement: Knowledge of (m, r, rho) such that: C1 = r*G, C2 = m*G + r*Pk, and PCm = m*G + rho*H.
- Parameters
-
ctx Pointer to a secp256k1 context object. proof [OUT] Pointer to 195-byte buffer for the proof output. c1 Pointer to the ElGamal C1 point (r*G). c2 Pointer to the ElGamal C2 point (m*G + r*Pk). pk Pointer to the recipient's public key. pcm Pointer to the Pedersen Commitment (m*G + rho*H). amount The plaintext amount (m). r The 32-byte secret ElGamal blinding factor. rho The 32-byte secret Pedersen blinding factor. context_id 32-byte unique transaction context identifier.
- Returns
- 1 on success, 0 on failure.
Definition at line 108 of file proof_link.c.
◆ secp256k1_elgamal_pedersen_link_verify()
| int secp256k1_elgamal_pedersen_link_verify | ( | const secp256k1_context * | ctx, |
| const unsigned char * | proof, | ||
| const secp256k1_pubkey * | c1, | ||
| const secp256k1_pubkey * | c2, | ||
| const secp256k1_pubkey * | pk, | ||
| const secp256k1_pubkey * | pcm, | ||
| const unsigned char * | context_id ) |
Verifies the link proof between ElGamal and Pedersen commitments.
- Returns
- 1 if the proof is valid, 0 otherwise.
Definition at line 212 of file proof_link.c.