Pedersen Commitments and NUMS Generator Derivation. More...
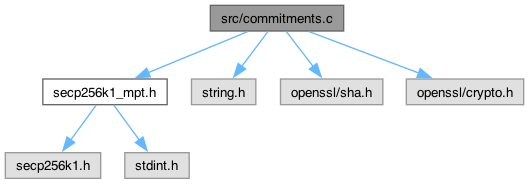
Go to the source code of this file.
Functions | |
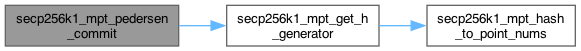
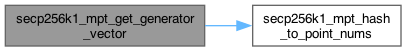
| int | secp256k1_mpt_hash_to_point_nums (const secp256k1_context *ctx, secp256k1_pubkey *out, const unsigned char *label, size_t label_len, uint32_t index) |
| Deterministically derives a NUMS (Nothing-Up-My-Sleeve) generator point. | |
| int | secp256k1_mpt_get_h_generator (const secp256k1_context *ctx, secp256k1_pubkey *h) |
| Derives the secondary base point (H) for Pedersen commitments. | |
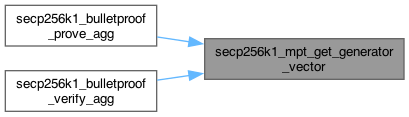
| int | secp256k1_mpt_get_generator_vector (const secp256k1_context *ctx, secp256k1_pubkey *vec, size_t n, const unsigned char *label, size_t label_len) |
| Generates a vector of N independent NUMS generators. | |
| int | secp256k1_mpt_pedersen_commit (const secp256k1_context *ctx, secp256k1_pubkey *commitment, uint64_t amount, const unsigned char *rho) |
| Creates a Pedersen Commitment C = amount*G + rho*H. | |
Detailed Description
Pedersen Commitments and NUMS Generator Derivation.
This module implements the core commitment scheme used in Confidential MPTs. It provides functions to generate Pedersen commitments of the form \( C = v \cdot G + r \cdot H \), where \( G \) and \( H \) are independent generators of the secp256k1 curve.
NUMS Generators: To ensure the binding property of the commitments (i.e., that a user cannot open a commitment to two different values), the discrete logarithm of \( H \) with respect to \( G \) must be unknown.
This implementation uses a "Nothing-Up-My-Sleeve" (NUMS) construction:
- Generators are derived deterministically using SHA-256 hash-to-curve.
- The domain separation tag is "MPT_BULLETPROOF_V1_NUMS".
- This guarantees that no backdoors exist in the system parameters.
Commitment Logic: The commitment function handles the edge case where the amount \( v = 0 \). Since the point at infinity (identity) cannot be serialized in standard compressed form, the term \( 0 \cdot G \) is handled logically, resulting in \( C = r \cdot H \).
- See also
- [Spec (ConfidentialMPT_20260201.pdf) Section 3.3.5] Linking ElGamal Ciphertexts and Pedersen Commitments
Definition in file commitments.c.
Function Documentation
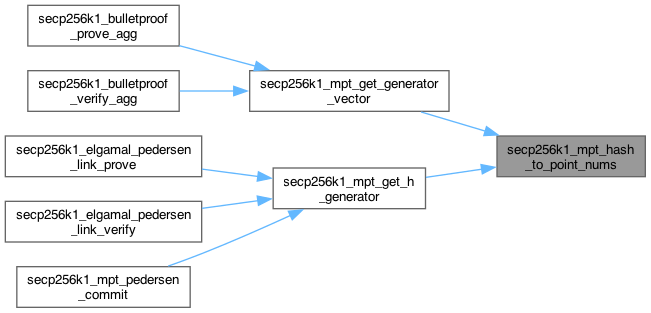
◆ secp256k1_mpt_get_generator_vector()
| int secp256k1_mpt_get_generator_vector | ( | const secp256k1_context * | ctx, |
| secp256k1_pubkey * | vec, | ||
| size_t | n, | ||
| const unsigned char * | label, | ||
| size_t | label_len ) |
Generates a vector of N independent NUMS generators.
- Used to populate the G_i and H_i vectors for Bulletproofs. Each point is derived deterministically from the provided label and its index.
- Parameters
-
ctx secp256k1 context. vec Array to store the resulting generators. n Number of generators to derive. label The label string ("G" or "H"). label_len Length of the label string.
- Returns
- 1 on success, 0 on failure.
Definition at line 124 of file commitments.c.
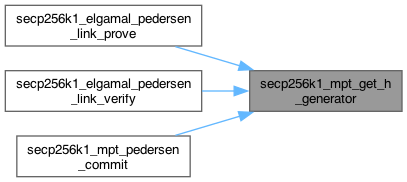
◆ secp256k1_mpt_get_h_generator()
| int secp256k1_mpt_get_h_generator | ( | const secp256k1_context * | ctx, |
| secp256k1_pubkey * | h ) |
Derives the secondary base point (H) for Pedersen commitments.
- This derives a NUMS point using the label "H" at index 0. This H is used alongside the standard generator G to form the commitment C = v*G + r*H. Using a NUMS point ensures that the discrete logarithm of H with respect to G is unknown.
- Parameters
-
ctx secp256k1 context. h The resulting H generator public key.
- Returns
- 1 on success, 0 on failure.
Definition at line 108 of file commitments.c.
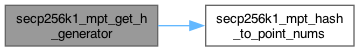
◆ secp256k1_mpt_hash_to_point_nums()
| int secp256k1_mpt_hash_to_point_nums | ( | const secp256k1_context * | ctx, |
| secp256k1_pubkey * | out, | ||
| const unsigned char * | label, | ||
| size_t | label_len, | ||
| uint32_t | index ) |
Deterministically derives a NUMS (Nothing-Up-My-Sleeve) generator point.
- Uses SHA-256 try-and-increment to find a valid x-coordinate. This ensures the discrete logarithm of the resulting point is unknown, which is a core security requirement for Bulletproof binding and vector commitments.
- Parameters
-
ctx secp256k1 context (VERIFY flag required). out The derived public key generator. label Domain/vector label (e.g., "G" or "H"). label_len Length of the label string. index Vector index (enforced Big-Endian).
- Returns
- 1 on success, 0 on failure.
Definition at line 48 of file commitments.c.
◆ secp256k1_mpt_pedersen_commit()
| int secp256k1_mpt_pedersen_commit | ( | const secp256k1_context * | ctx, |
| secp256k1_pubkey * | commitment, | ||
| uint64_t | amount, | ||
| const unsigned char * | rho ) |
Creates a Pedersen Commitment C = amount*G + rho*H.
- Parameters
-
ctx secp256k1 context. commitment Output commitment public key. amount The value to commit to. rho The blinding factor (randomness).
- Returns
- 1 on success, 0 on failure.
Definition at line 149 of file commitments.c.